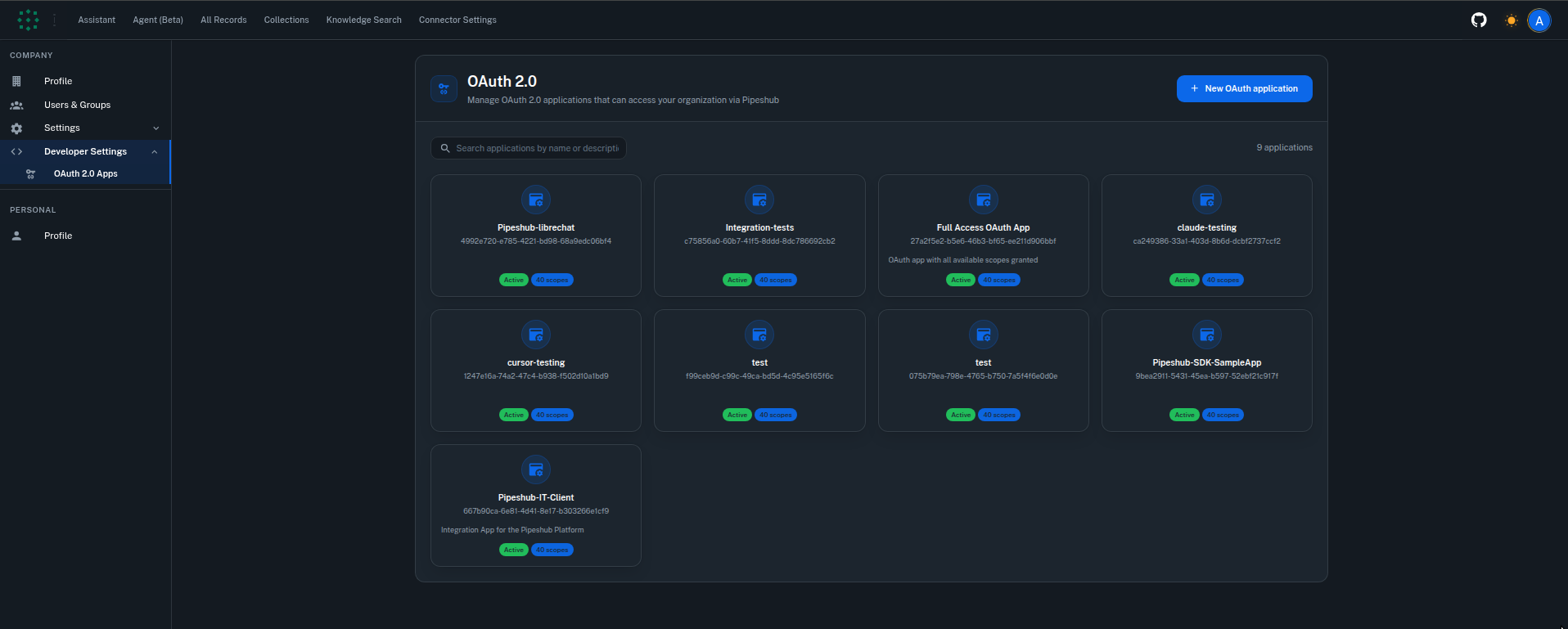
Who Can Manage OAuth Applications
OAuth application management is available exclusively to administrators. Only users with admin privileges can create, edit, suspend, or delete OAuth applications within the organization.Navigating to OAuth Settings
To access the OAuth application management page:- Sign in to your PipesHub account with administrator credentials
- Navigate to Connector Settings from the Navbar
- Select OAuth 2.0 Apps under the Developer Settings section
Creating a New OAuth Application
Follow these steps to register a new OAuth application.Step 1: Open the Application Registration Form
From the OAuth 2.0 Apps page, click the New OAuth application button.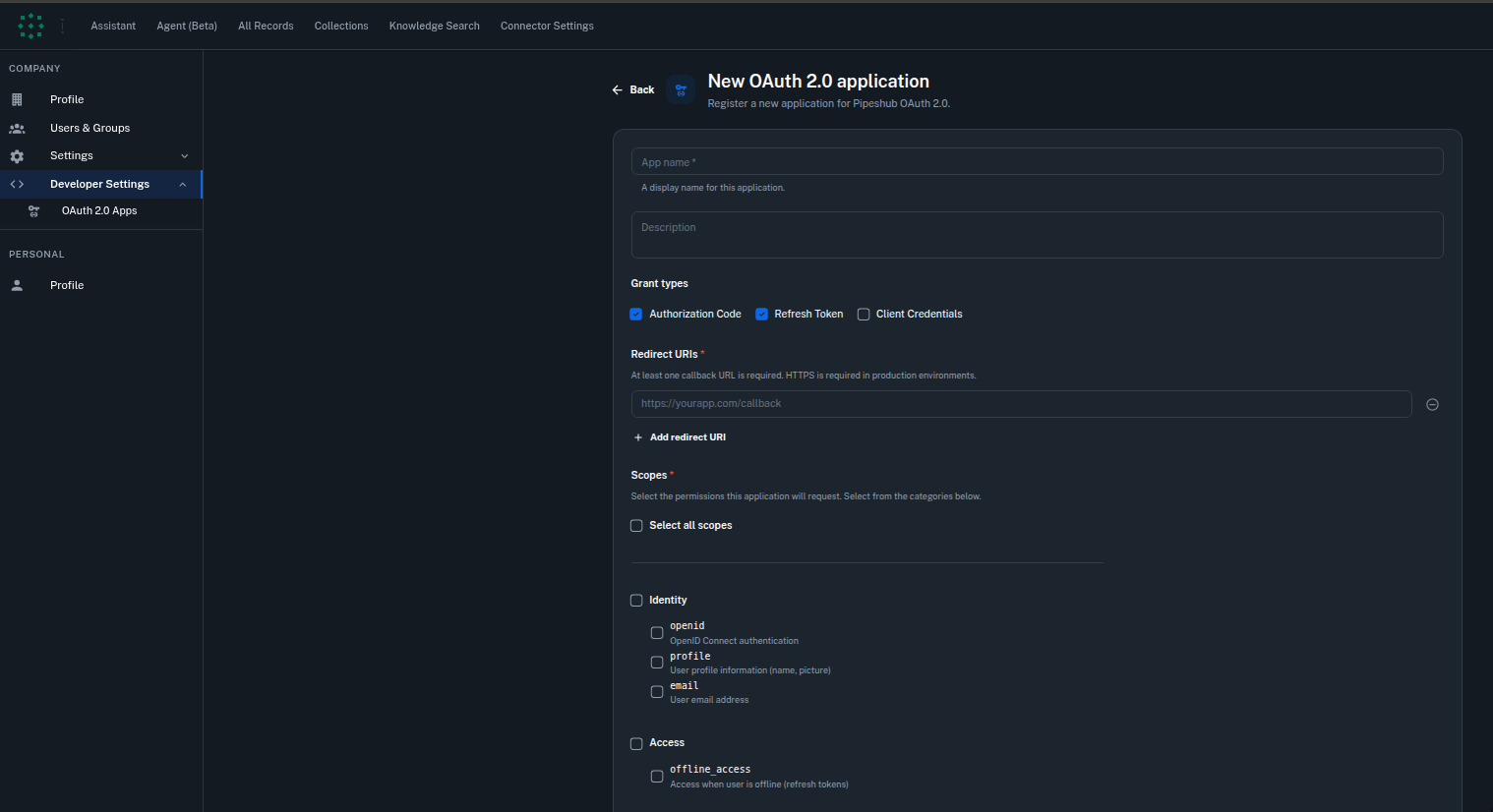
Step 2: Provide Application Details
Fill in the following fields:| Field | Required | Description |
|---|---|---|
| Application Name | Yes | A descriptive name for the application (1-100 characters). This name is displayed to users during the consent process. |
| Description | No | A brief explanation of what the application does (up to 500 characters). Helps users understand why they are granting access. |
| Homepage URL | No | The URL of the application’s homepage or landing page. |
| Privacy Policy URL | No | Link to the application’s privacy policy. |
| Terms of Service URL | No | Link to the application’s terms of service. |
Step 3: Configure Grant Types
Select the authorization grant types that your application requires:Authorization Code (Recommended)
Authorization Code (Recommended)
Client Credentials
Client Credentials
- Background services or automation scripts
- Machine-to-machine integrations
- Scheduled tasks that access organizational data
Refresh Token
Refresh Token
offline_access scope is requested during the authorization code flow.Key details:- Refresh tokens are rotated on each use — the old token is revoked and a new one is issued
- Your application should always store the latest refresh token
- Refresh tokens have a default lifetime of 30 days (configurable per application)
Step 4: Add Redirect URIs
Redirect URIs define where PipesHub sends users after they authorize (or deny) access. You may register up to 10 redirect URIs per application.
- All redirect URIs must use HTTPS, except for
localhostand127.0.0.1(permitted for local development) - The URI provided during the authorization request must exactly match one of the registered URIs
- Redirect URIs are required when the Authorization Code grant type is enabled
Step 5: Select Scopes
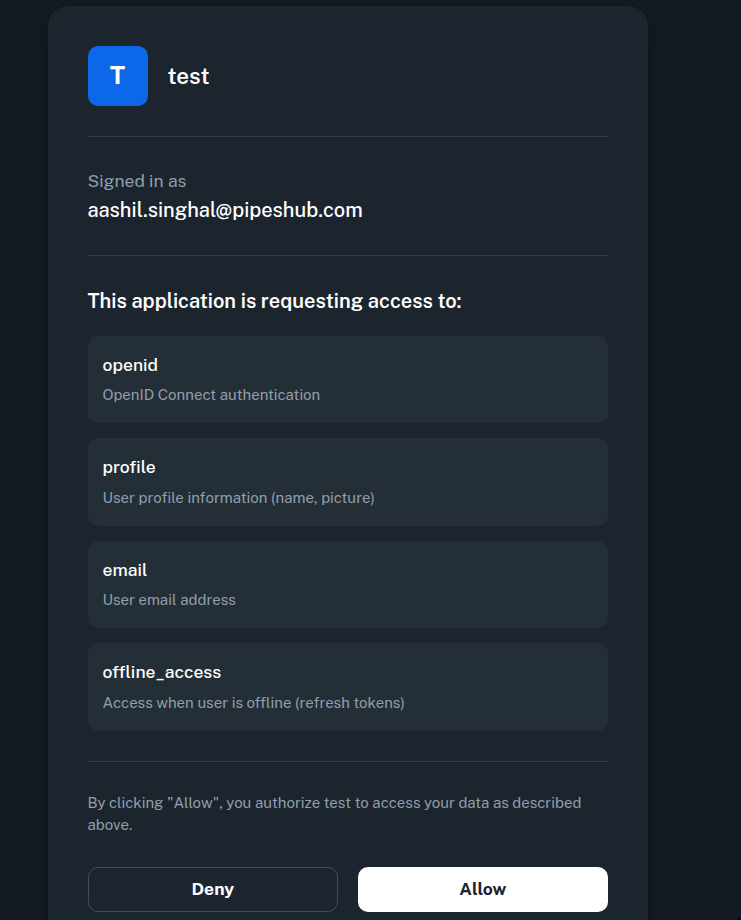
Scopes define the specific permissions your application is requesting. Select only the scopes your application genuinely needs — following the principle of least privilege.
Identity & Access Scopes
Identity & Access Scopes
| Scope | Description |
|---|---|
openid | Required for OpenID Connect. Returns a unique user identifier. |
profile | Access to the user’s basic profile information. |
email | Access to the user’s email address. |
offline_access | Enables refresh tokens for long-lived sessions without repeated user consent. |
Organization Scopes
Organization Scopes
| Scope | Description |
|---|---|
org:read | View organization details and settings. |
org:write | Modify organization settings and configuration. |
org:admin | Full administrative access to organization management. |
User Management Scopes
User Management Scopes
| Scope | Description |
|---|---|
user:read | View user profiles and details. |
user:write | Modify user information and settings. |
user:invite | Invite new users to the organization. |
user:delete | Remove users from the organization. |
User Groups & Teams Scopes
User Groups & Teams Scopes
| Scope | Description |
|---|---|
usergroup:read | View user groups and their members. |
usergroup:write | Create, modify, or delete user groups. |
team:read | View team information. |
team:write | Create, modify, or delete teams. |
Knowledge Base Scopes
Knowledge Base Scopes
| Scope | Description |
|---|---|
kb:read | View knowledge base content and records. |
kb:write | Create and modify knowledge base content. |
kb:delete | Delete knowledge base records. |
kb:upload | Upload files and documents to the knowledge base. |
Search & Conversations Scopes
Search & Conversations Scopes
| Scope | Description |
|---|---|
semantic:read | Perform semantic search queries. |
semantic:write | Create and modify search indexes. |
semantic:delete | Delete search indexes or entries. |
conversation:read | View conversations and chat history. |
conversation:write | Create and modify conversations. |
conversation:chat | Send messages and interact in real-time conversations. |
Agents Scopes
Agents Scopes
| Scope | Description |
|---|---|
agent:read | View agent configurations and details. |
agent:write | Create and modify agent configurations. |
agent:execute | Execute agents and trigger agent workflows. |
Connectors Scopes
Connectors Scopes
| Scope | Description |
|---|---|
connector:read | View connector configurations and status. |
connector:write | Create and modify connector configurations. |
connector:sync | Trigger data synchronization for connectors. |
connector:delete | Remove connector instances. |
Configuration & Storage Scopes
Configuration & Storage Scopes
| Scope | Description |
|---|---|
config:read | View system configuration settings. |
config:write | Modify system configuration settings. |
document:read | Read files and documents from storage. |
document:write | Upload and modify files in storage. |
document:delete | Delete files from storage. |
Crawling Scopes
Crawling Scopes
| Scope | Description |
|---|---|
crawl:read | View crawling jobs and their status. |
crawl:write | Create and modify crawling jobs. |
crawl:delete | Delete crawling jobs. |
Step 6: Save and Store Credentials
After submitting the form, PipesHub generates a unique Client ID and Client Secret for your application.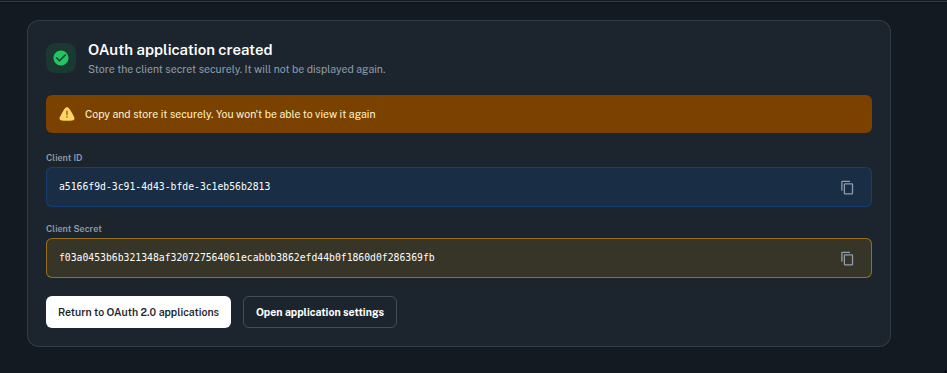
Authorization Flow
The following diagram illustrates how the OAuth 2.0 Authorization Code flow operates within PipesHub.Step-by-Step Breakdown
Initiate Authorization
User Authentication
User Consent
Authorization Code
Exchange Code for Tokens
code_verifier instead of client_secret:Client Credentials Flow
For server-to-server integrations that do not require user context:Refreshing Tokens
When an access token expires, use the refresh token to obtain a new one without requiring user interaction:Revoking Tokens
To revoke an access token or refresh token when it is no longer needed:token_type_hint to either access_token or refresh_token to help the server identify the token type more efficiently.
OpenID Connect Discovery
PipesHub supports OpenID Connect Discovery, enabling clients to automatically discover OAuth endpoints and configuration:| Endpoint | URL |
|---|---|
| OpenID Configuration | /.well-known/openid-configuration |
| OAuth Authorization Server Metadata | /.well-known/oauth-authorization-server |
| JSON Web Key Set (JWKS) | /.well-known/jwks.json |
Managing OAuth Applications
Viewing Application Details
Click on any application from the list to view its configuration, including the client ID, allowed scopes, grant types, redirect URIs, and token settings.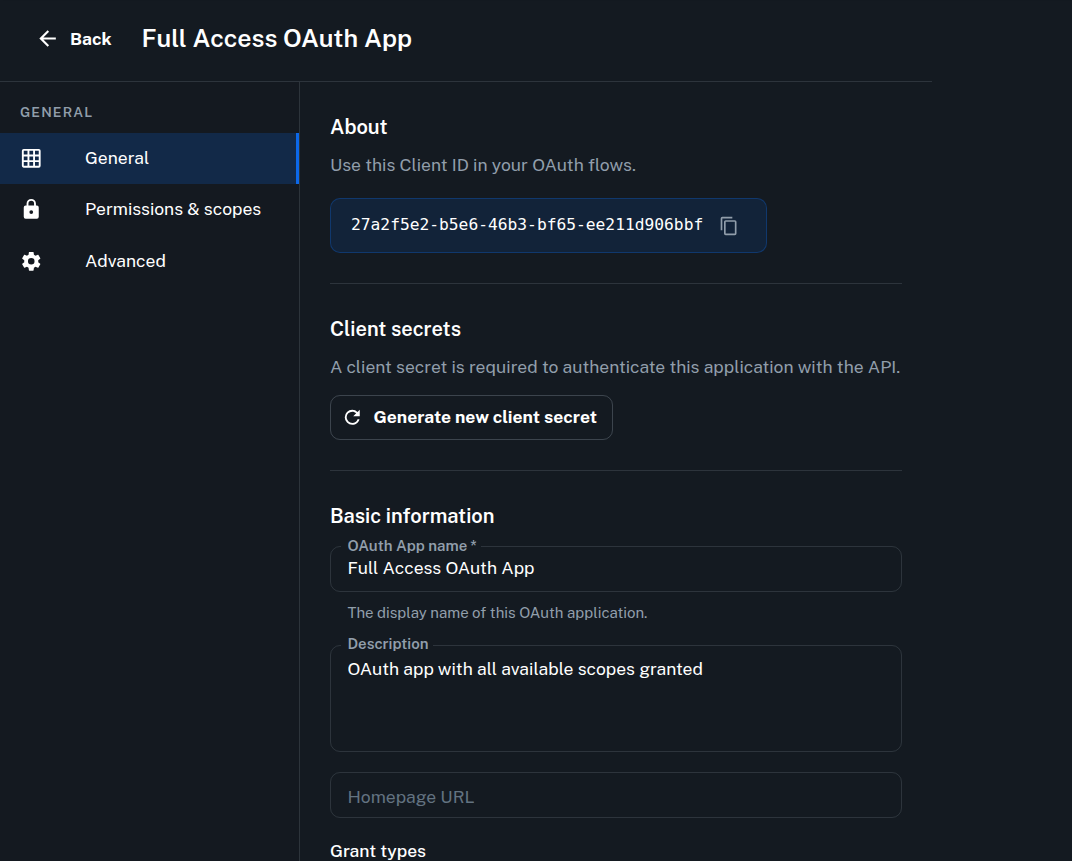
Regenerating the Client Secret
If your client secret has been compromised or needs to be rotated:- Open the application detail page
- Click Generate new client secret
- Copy and securely store the new secret immediately
Suspending an Application
If you need to temporarily disable an application without deleting it:- Open the application detail page
- Go to Advanced section in sidebar
- Click Suspend Application
Deleting an Application
Deleting an OAuth application:- Revokes all active access tokens and refresh tokens associated with the application
- Permanently marks the application as revoked
- Open the application detail page
- Go to Advanced section in sidebar
- Click Delete Application
- Confirm by putting the application name in dialog box
Revoking Active Tokens
From the application detail page, administrators can:- Revoke all tokens at once, which is useful in the event of a security incident
- Open the application detail page
- Go to Advanced section in sidebar
- Click Revoke all tokens
- Confirm by putting the application name in dialog box
Security Best Practices
Store Secrets Securely
Use PKCE for Public Clients
Request Minimal Scopes
Validate the State Parameter
state value for each authorization request and verify it in the callback to prevent cross-site request forgery (CSRF) attacks.Handle Token Rotation
Revoke Tokens on Sign-Out
API Endpoints Reference
The following table provides a quick reference for all OAuth 2.0 endpoints:| Endpoint | Method | Description |
|---|---|---|
/api/v1/oauth2/authorize | GET | Initiate the authorization flow |
/api/v1/oauth2/authorize | POST | Submit user consent |
/api/v1/oauth2/token | POST | Exchange code for tokens, refresh tokens, or client credentials |
/api/v1/oauth2/revoke | POST | Revoke an access or refresh token |
/api/v1/oauth2/introspect | POST | Inspect a token’s validity and metadata |
/api/v1/oauth2/userinfo | GET | Retrieve user profile information (requires openid scope) |
/.well-known/openid-configuration | GET | OpenID Connect Discovery document |
/.well-known/jwks.json | GET | Public keys for token verification |
Troubleshooting
Authorization request returns an error
Authorization request returns an error
Token exchange fails with 'invalid_grant'
Token exchange fails with 'invalid_grant'
- The authorization code has expired (codes are valid for 10 minutes)
- The authorization code has already been used
- The
redirect_uriin the token request does not match the one used during authorization - For PKCE: the
code_verifierdoes not match the originalcode_challenge
Refresh token is rejected
Refresh token is rejected
- The refresh token has been rotated and the old token was used instead of the most recent one
- The refresh token has expired
- The application or its tokens have been revoked by an administrator
API request returns 403 Forbidden
API request returns 403 Forbidden
- The access token does not include the required scope for the requested endpoint
- The user does not have sufficient permissions within the organization
FAQ
Can non-admin users create OAuth applications?
Can non-admin users create OAuth applications?
What happens when I regenerate a client secret?
What happens when I regenerate a client secret?
Is there a limit on the number of OAuth applications?
Is there a limit on the number of OAuth applications?
Does PipesHub support PKCE?
Does PipesHub support PKCE?
S256 and plain challenge methods, though S256 is strongly recommended.